It has been confirmed that the most frequently used keyword type in phishing emails in the second quarter of this year was 'Payment·Purchase.'
On the 14th, AhnLab announced the '2024 2nd Quarter Phishing Email Statistics Report,' which analyzed phishing emails and attachments collected during the second quarter by type.
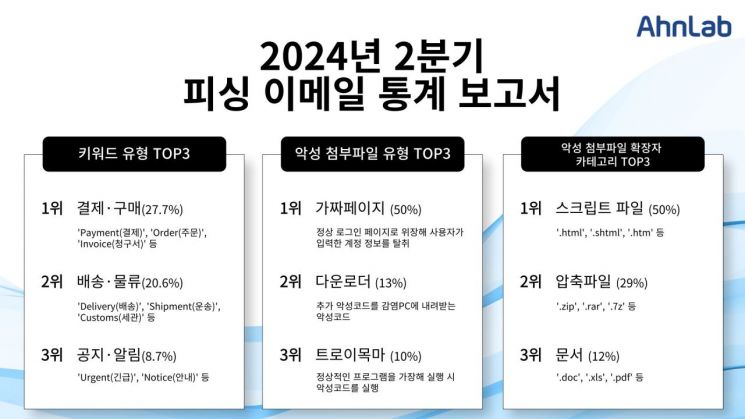
The keyword type most used in phishing emails, Payment·Purchase, accounted for 27.7% of the total. Attackers included keywords related to financial transactions such as 'Payment,' 'Order,' and 'Invoice' in the subject lines to attract users' attention.
Next, keywords related to 'Delivery·Logistics' recorded 20.6%. They used words like 'Delivery,' 'Shipment,' and 'Customs,' or impersonated by mentioning actual well-known logistics companies.
The 'Notice·Alert' keyword type ranked third with 8.7%. This type exploits users' anxious psychology and curiosity using keywords such as 'Urgent' and 'Notice.'
AhnLab explained that all these keyword types are highly relevant to work and daily life, and since overseas direct purchases through Chinese e-commerce have recently become popular, users need to exercise special caution.
Additionally, AhnLab's analysis of attachment types in phishing emails during the second quarter found that the 'Fake Page' type accounted for 50%, the highest proportion. Fake pages imitate various elements of legitimate pages such as layout, logos, and fonts. They mainly disguise themselves as login pages to induce users to enter their account information, which is then sent to the attacker's server.
Also identified was the 'Downloader,' which downloads additional malware onto infected PCs, accounting for 13%. Following this were 'Trojan' (10%), which disguises itself as legitimate programs but executes malware upon running, and 'Infostealer' (5%), which steals user information.
Programs designed to install malware on systems, such as 'Dropper,' and 'Adware' that automatically displays advertisements upon installation, which were not detected in the first quarter, were also partially detected.
The most frequently used attachment file extension category in phishing emails was 'Script Files (50%).' Script files are used to run fake pages in web browsers and include extensions such as '.html,' '.shtml,' and '.htm.'
The second most used attachment file extension type was 'Compressed Files (29%).' Extensions include '.zip,' '.rar,' and '.7z,' and attackers are presumed to use compressed file formats to conceal malicious executable files. When malicious files distributed with these extensions are decompressed, users are exposed to various malware such as downloaders and infostealers.
The next most frequently found malicious attachments were 'Documents,' including extensions such as '.doc,' '.xls,' and '.pdf,' accounting for 12% of the total. Malicious documents require extra caution as users may inadvertently execute them.
To prevent damage caused by phishing emails, users should ▲verify the sender of emails and avoid opening attachments or URLs in suspicious emails ▲use different accounts for each site and change passwords regularly ▲keep antivirus programs like V3 updated to the latest version and enable phishing site blocking features ▲maintain the latest versions of programs in use and apply security patches.
Meanwhile, AhnLab provides professional and up-to-date threat information, including IoCs (Indicators of Compromise) related to phishing email attacks, through its next-generation threat intelligence platform 'AhnLab TIP.'
© The Asia Business Daily(www.asiae.co.kr). All rights reserved.
![Clutching a Stolen Dior Bag, Saying "I Hate Being Poor but Real"... The Grotesque Con of a "Human Knockoff" [Slate]](https://cwcontent.asiae.co.kr/asiaresize/183/2026021902243444107_1771435474.jpg)