Ministry of Science and ICT-KISA Announce Cyber Threat Trends
"Increase in Sophisticated Attacks... Public and Businesses Urged to Be Cautious"
Cyber intrusion incidents in the first half of this year increased by 40% compared to the same period last year. Phishing attacks that previously impersonated acquaintances have evolved into sophisticated attacks targeting messenger accounts such as Telegram.
The Ministry of Science and ICT, together with the Korea Internet & Security Agency (KISA), announced the major cyber threat trends for the first half of this year on the 31st.
The Ministry of Science and ICT stated, "Recently, attackers are actively identifying targets and conducting sophisticated attacks by thoroughly analyzing vulnerabilities in personal and corporate systems and mobile devices," urging "special caution from the public and businesses."
Looking at intrusion incident report statistics over the past three years, the number increased from 640 cases in 2021 to 1,142 cases last year, nearly doubling year-on-year. The number of intrusion incident reports in the first half of this year was 664, about 40% higher than the same period last year.
The proportion of intrusion incident reports from the manufacturing sector increased by 62.5% compared to the first half of last year. It is analyzed that attackers are focusing on small businesses with low security levels.
Analysis of domestic intrusion incidents in the first half of this year revealed four major characteristics.
First, attackers prioritized locating backup servers to advance ransomware attacks.
Attackers find vulnerabilities in servers connected to the internet that are exposed externally and easily accessible, then infiltrate internally. While stealing data, they primarily locate backup servers to encrypt data and demand ransom through a complex method (multiple threats), thereby advancing ransomware attacks.
Companies must block abnormal access and eliminate security vulnerabilities on externally exposed servers. They should thoroughly manage attack surfaces by removing threat entry points that allow internal infiltration. Backup servers should be set up in separate environments such as network segmentation.
The second characteristic is the increase in sophisticated cyberattacks by professional hacking groups targeting security software (SW) vulnerabilities.
Attacks exploiting vulnerabilities in security software used internally, such as network monitoring programs, have been repeatedly discovered. These attacks infect employee PCs through the software, install malware for remote control, and take over internal networks.
This attack method is harder to detect than traditional malware email attacks and is considered highly threatening because victims may not even realize they have been attacked.
The Ministry of Science and ICT and KISA are continuously tracking these attacks, which are believed to be carried out by professional hacking groups backed by foreign states, through joint investigations with related agencies. They are also taking urgent measures to prevent further damage by promptly applying security patches.

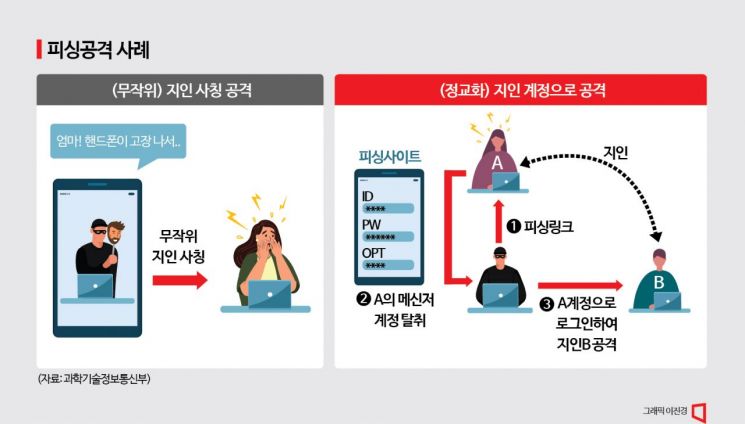
The third characteristic is the spread of phishing attacks using stolen accounts that appear to be sent directly by acquaintances, going beyond simple impersonation.
The pattern of phishing site attacks, which previously involved impersonating acquaintances or security officials to steal personal information from unspecified users, has recently changed.
Attacks are shifting to target messenger accounts such as Telegram, analyzed as attempts to steal conversation contents and personal information stored in messenger programs.
Attackers access the victim’s messenger account and request personal information such as phone numbers and verification codes from registered friends, family, and acquaintances. Recipients of these messages may easily be deceived into believing they were sent by the actual account user.
The Ministry of Science and ICT and KISA are working with telecommunications companies to urgently block phishing sites that induce personal information input and provide guidance on checking for damage and response methods through the BohoNara website and the 118 reporting hotline.
Users are advised to enable two-factor authentication on messenger programs like Telegram and avoid accessing sites of unclear origin.
The fourth characteristic is the increase in security incidents caused by careless developers, such as sharing administrator accounts.
Attacks exploiting security management weaknesses are increasing, where system developers or maintenance personnel within companies share administrator accounts for websites or cloud services for convenience or allow direct access to critical internal systems via virtual private networks (VPNs).
Companies must ensure that not only system administrators but also a small number of developers and maintenance personnel strictly follow security protocols. They should carefully manage security policies by minimizing permissions and access devices during remote access via VPNs.
The Ministry of Science and ICT stated, "We will prepare a software supply chain security guideline within the year to support the establishment of a new security system," and added, "We are preparing to announce measures by August to enhance information protection capabilities for small and medium-sized enterprises and individuals in cyber security blind spots, as well as industrial development plans to strengthen the information protection industry."
© The Asia Business Daily(www.asiae.co.kr). All rights reserved.
![Clutching a Stolen Dior Bag, Saying "I Hate Being Poor but Real"... The Grotesque Con of a "Human Knockoff" [Slate]](https://cwcontent.asiae.co.kr/asiaresize/183/2026021902243444107_1771435474.jpg)