Third under Yoon Administration, First in Cyber Sector
Hacking and Virtual Asset Theft... Funding for Nuclear and Missile Programs
Ministry of Foreign Affairs "Leading International Response with Comprehensive Sanctions"
[Asia Economy Reporter Jang Hee-jun] The government has designated hackers and their backing organizations that have been financing North Korea's nuclear and missile development as targets for sanctions. This is the first independent sanction in the cyber sector aimed at North Korea.
The Ministry of Foreign Affairs announced on the 10th that it will designate four North Korean individuals and seven institutions involved in illegal cyber activities such as hacking and virtual asset theft, as well as those involved in developing related programs and training specialized personnel, as independent sanction targets.
 Lee Jun-il, Head of the North Korea Nuclear Diplomacy Planning Team, is explaining on the 10th at the Ministry of Foreign Affairs about the designation of North Korean individuals and organizations involved in illegal cyber activities to fund nuclear and missile development as independent sanction targets.
Lee Jun-il, Head of the North Korea Nuclear Diplomacy Planning Team, is explaining on the 10th at the Ministry of Foreign Affairs about the designation of North Korean individuals and organizations involved in illegal cyber activities to fund nuclear and missile development as independent sanction targets. [Image source=Yonhap News]
Lee Jun-il, head of the North Korea Nuclear Diplomacy Planning Division at the Ministry of Foreign Affairs, said at a briefing on the same day, "The government will make every effort to protect the security of our citizens and the assets of people worldwide and block North Korea's illegal cyber activities."
Lee emphasized, "As international sanctions have been strengthened, North Korea has closed its borders since COVID-19 and has been focusing on illegal cyber foreign currency earning. A significant portion of the funds earned this way is invested in nuclear and missile development, threatening us with a nuclear preemptive strike and engaging in various provocations."
As North Korea increased hacking attacks such as virtual asset theft to circumvent sanctions and finance nuclear and missile development, the government moved to block these activities. This measure is the third independent sanction under the Yoon Seok-yeol administration and the first-ever sanction in the cyber sector. Previously, in October and December of last year, targets involved in North Korea's nuclear and missile development and evasion of sanctions were successively designated for independent sanctions.
Four individuals and seven institutions... "Leading the international community's response to North Korea's nuclear threat"
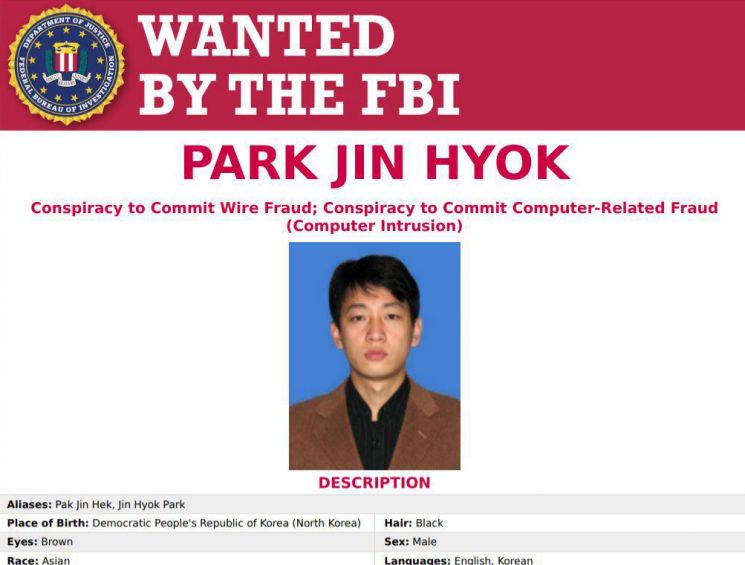 North Korean 'hacker' Park Jin-hyuk indicted in the United States. Photo shows the FBI wanted poster for North Korean hacker Park Jin-hyuk. [Image source=Yonhap News]
North Korean 'hacker' Park Jin-hyuk indicted in the United States. Photo shows the FBI wanted poster for North Korean hacker Park Jin-hyuk. [Image source=Yonhap News]
The North Korean hackers listed on the government's sanction list on this day are Park Jin-hyeok, Jo Myung-rae, Song Rim, and Oh Choong-sung. The institutions and organizations include Chosun Expo Joint Venture Company, Lazarus Group, BlueNoroff, Andariel, Reconnaissance General Bureau, Laboratory No. 110, and Command Automation University (Mirim University), totaling seven.
Park Jin-hyeok is a hacker affiliated with Chosun Expo Joint Venture Company and was involved in the 2014 Sony Pictures hack in the U.S. and the 2017 WannaCry ransomware attack. Jo Myung-rae is the head of the Computer Technology Research Institute under the Reconnaissance General Bureau and developed the network attack virus 'JML'. Song Rim belongs to the Hapjanggang Trading Company under the Rocket Industry Department and produced and sold a voice phishing app for smartphones, while Oh Choong-sung is an IT personnel affiliated with the Ministry of Defense who developed and provided IT programs to multiple companies through recruitment platforms in places like Dubai.
Among the sanctioned institutions, Command Automation University is understood to be involved in training and dispatching North Korean cyber specialists. Established in 1986 under the General Staff Department of the People's Army, Command Automation University produces about 100 cyber specialists annually. The other independently sanctioned institutions participated in cyber attacks such as hacking and virtual asset theft. In particular, Laboratory No. 110 is a hacker organization under the People's Army Reconnaissance Bureau, established in the early 2000s, and is a unit dedicated to cyber warfare.
Notably, the globally notorious Lazarus Group also had eight virtual asset wallet addresses included in the sanctions list. Additionally, among the sanctioned targets, Jo Myung-rae, Song Rim, Oh Choong-sung, as well as the Reconnaissance General Bureau, Laboratory No. 110, and Command Automation University, are subjects of sanctions for the first time in the world by South Korea.
This is interpreted as a determination to lead the international community's sanctions against North Korea, breaking away from the previous pattern of following sanctions imposed by the U.S. or the European Union (EU). Lee Jun-il stated, "We will comprehensively sanction North Korea's cyber activities, including backing organizations that other countries have not yet sanctioned, and lead the international community's response."
Government: "Will create synergy through international cooperation and public-private collaboration"
 North Korean Cyber Attacks
North Korean Cyber Attacks
The government plans to actively engage in international cooperation and public-private collaboration to suppress North Korea's illegal cyber activities in the future.
An official from the Ministry of Foreign Affairs told reporters on the day, "(To enhance the effectiveness of this sanction measure) we are closely consulting and cooperating with the international community," adding, "Public-private collaboration is a field where synergy can be created. Because technology develops rapidly and methods vary, it will be effective to gather wisdom from experts across various fields for research to block these activities effectively."
In particular, the official hinted that additional sanctions in the cyber sector and the inclusion of more virtual asset wallet addresses on the sanction list are under continuous review, indicating that sanctions against North Korea in the cyber sector will continue.
This measure is based on the Foreign Exchange Transactions Act and the Act on the Prohibition of Fund-Raising for the Purpose of Threatening the Public or Proliferation of Weapons of Mass Destruction. Those designated as financial sanction targets must obtain prior approval from the Governor of the Bank of Korea or the Financial Services Commission to conduct foreign exchange or financial transactions. Transactions without approval may be punished under relevant laws, and trading virtual assets with sanctioned entities without prior approval from the Financial Services Commission is also prohibited.
Meanwhile, according to the National Intelligence Service, the average daily number of attack attempts by international and state-backed hacking organizations reaches 1.15 million. The intelligence authorities assess that many of these are the work of North Korea. The damage caused by North Korea's cyber attacks worldwide is estimated to have exceeded 1.5 trillion won since 2017.
The National Intelligence Service also announced a security advisory on the same day, jointly with U.S. intelligence agencies such as the National Security Agency (NSA) and the Federal Bureau of Investigation (FBI), to inform about North Korea's cyber threat status and to prevent it. The advisory warned that North Korea targets major institutions in various sectors worldwide with ransomware attacks aiming to steal virtual assets. This is the first security advisory jointly issued by South Korean and U.S. intelligence agencies.
© The Asia Business Daily(www.asiae.co.kr). All rights reserved.
![Clutching a Stolen Dior Bag, Saying "I Hate Being Poor but Real"... The Grotesque Con of a "Human Knockoff" [Slate]](https://cwcontent.asiae.co.kr/asiaresize/183/2026021902243444107_1771435474.jpg)