North Korean hacking group 'Lazarus' suspected by methods
Confirmed leaked data 0.5%... Difficult to estimate damage scale
A group suspected to be a North Korean hacking organization infiltrated the domestic court's computer network and extracted over 1000GB (gigabytes) of data containing personal information over a period of more than two years. This has brought to light issues regarding the judiciary's security management and response system, which handles sensitive personal information.
The National Police Agency's National Investigation Headquarters (NIH) disclosed on the 11th the results of a joint investigation and probe with the National Intelligence Service and the prosecution into the court network hacking and data leakage incident that surfaced at the end of last year.
According to the investigation, the intrusion into the court network occurred from before January 7, 2021, until February 9 of last year, when the attacker’s malicious program was detected by antivirus software. During this period, a total of 1014GB of court data was transmitted outside the court network through eight servers (four domestic and four overseas).
However, since the Supreme Court responded internally, the police investigation only began on December 5 of last year, after the hacking incident was first reported by the media. Because the investigation started long after the intrusion, the hacking route and purpose could not be confirmed.
An NIH official stated, “Among the installation dates of the malicious programs, January 7, 2021, was confirmed as the earliest. The attacker must have infiltrated the court network before this date, but detailed records from the security equipment at that time had already been deleted, so the initial intrusion time and cause could not be identified.”
The investigative authorities restored records left on one domestic server and confirmed that 5,171 files (4.7GB) related to rehabilitation cases were leaked. This accounts for only 0.5% of the total. The leaked materials included handwritten statements, debt increase and insolvency reports, marriage certificates, medical certificates, etc., containing numerous personal details such as names, resident registration numbers, financial information, and medical history. The other seven servers had already expired their data retention periods, making it impossible to find traces.
To prevent secondary damage, the police provided the 5,171 leaked files to the Court Administration Office on the 8th and instructed them to notify the victims. The NIH stated that the court, upon receiving the leaked data, would determine whether personal information was involved and estimate the number of victims, but due to the limited data confirmed, it is expected to be difficult to accurately estimate the actual scale of the damage.
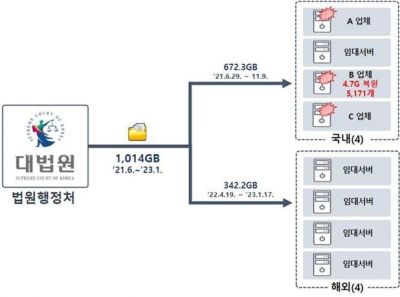 Overview of the Court Network Hacking and Data Leakage Incident
Overview of the Court Network Hacking and Data Leakage Incident [Image source: Provided by the National Police Agency]
Based on the type of program used in the crime, payment records for rented servers using virtual assets, IP addresses, and other evidence, the investigative authorities concluded that the incident was the work of the North Korean hacking group ‘Lazarus.’ The NIH stated, “Comparing and analyzing this case with previously identified North Korean hacking incidents, we confirmed that the Lazarus group’s commonly used LazarDoor malware and server hacking techniques mostly matched.”
There are also criticisms that the court’s security system is lax because the antivirus program detected the malware belatedly. An NIH official explained, “Generally, hackers confirm that their malware is not detected by antivirus software before distributing it, so it is difficult to criticize the antivirus program’s performance itself. It should be seen as detection resulting from antivirus program updates.”
Regarding whether the court’s personal information managers will be punished, the official added, “There are no punishment provisions under the Personal Information Protection Act, only administrative measures such as fines and penalties. If an investigation is necessary, it would be conducted by the Personal Information Protection Commission, and if there is suspicion of dereliction of duty, the court can make its own judgment and request an investigation by law enforcement agencies.”
© The Asia Business Daily(www.asiae.co.kr). All rights reserved.