Disguised as Itaewon Accident Report to Distribute Malware
Posing as Recovery Emails During October 'Kakao Outage' Attack
 North Korean hacking group 'APT37' impersonates Itaewon disaster report to distribute malware [Image source=Yonhap News]
North Korean hacking group 'APT37' impersonates Itaewon disaster report to distribute malware [Image source=Yonhap News]
[Asia Economy Reporter Jang Hee-jun] North Korea launched a cyberattack exploiting the 'Itaewon tragedy.' Following the hacking emails distributed during the 'Kakao outage' incident in October, it once again utilized a Korean social issue for a cyberattack.
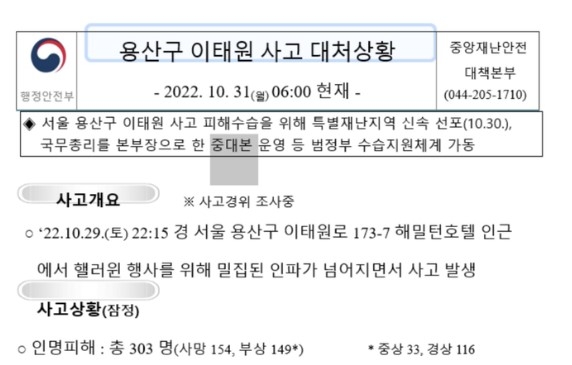
Google's Threat Analysis Group (TAG) revealed in a report published on its website on the 8th that at the end of October, the North Korean hacking group 'APT37' embedded malware in a Word file titled 'Yongsan-gu Itaewon Incident Response Status - 2022.10.31(Mon) 06:00 Current' and distributed it.
The file was crafted to imitate the format of the Central Disaster and Safety Countermeasures Headquarters report and contained detailed information about the incident overview, casualties, and response status.
TAG pointed out, "The file refers to the tragic event that occurred in Itaewon, Seoul, on October 29, 2022," and added, "It exploited the widespread public interest in the incident as bait."
In fact, North Korea has recently shown a pattern of sophisticatedly exploiting Korean social issues. Earlier in October, when a fire at the SK C&C Pangyo data center caused Kakao service disruptions, phishing emails titled '[Kakao] Partial Service Error Recovery and Emergency Measures Notice' were sent targeting North Korea-related industry workers, defectors, and politicians.
The malware distributed by APT37 this time has not been specifically identified yet, but this group has a history of distributing malware such as Dolphin and Bluelight.
APT37 is known by various names including 'Kimsung121,' 'ScarCraft,' 'Red Eyes,' and 'Group123.' It is an organization that has attacked domestic North Korea-related groups and defense sector personnel using the latest security vulnerabilities. Previously, in 2019, it distributed malware embedded in emails disguised as Ministry of Unification clarification materials, and in 2018, it spread malicious smartphone files disguised as the Naver Vaccine app.
© The Asia Business Daily(www.asiae.co.kr). All rights reserved.
![Clutching a Stolen Dior Bag, Saying "I Hate Being Poor but Real"... The Grotesque Con of a "Human Knockoff" [Slate]](https://cwcontent.asiae.co.kr/asiaresize/183/2026021902243444107_1771435474.jpg)