Kim Cheol-ung, President of the Financial Security Institute, Holds Emergency Inspection Meeting
Disseminates Urgent Situation and Distributes Vulnerability Detection Rules
Large-Scale Attack Targeting Financial Companies Unlikely
Domestic Security Firms Respond Swiftly

[Asia Economy Reporters Nahum Kang and Seungseop Song] It has been confirmed that domestic financial companies were also included in the random attacks exploiting the ‘Log4j’ vulnerability, considered the worst security flaw in computer history. Although the attacks were exploratory in nature, targeting vulnerable servers with low risk and no damage reported, experts emphasize the need for special caution as breaches could cause significant harm to companies and consumers.
According to the financial sector on the 13th, the Financial Security Institute held an emergency inspection meeting chaired by Director Kim Cheol-woong the previous day. This was due to the detection of Log4j-related attacks targeting servers of domestic financial companies. No successful hacking or damage cases have been confirmed yet. The scale and frequency of the attacks have not been disclosed in detail.
During the meeting, the Financial Security Institute analyzed the impact on the financial sector and reviewed the response status. They issued emergency communication measures to each financial company and developed and rapidly distributed rules to detect vulnerabilities.
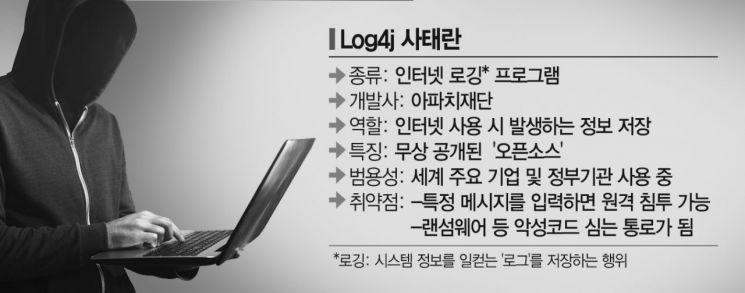
Log4j is a program used on the internet to record ‘logs.’ Logs are information generated while using a computer, and Log4j serves to store these logs. Developed by the Apache Foundation, it is essential for server management. As an open-source program provided free of charge, it is used by major global companies and government agencies such as Apple and Amazon.
 Video game screen of 'Minecraft' developed by Mojang Studios, a Swedish developer. Photo by Minecraft official website
Video game screen of 'Minecraft' developed by Mojang Studios, a Swedish developer. Photo by Minecraft official website
Log4j became controversial recently when a vulnerability allowing hackers to infiltrate was discovered in the game ‘Minecraft.’ The game uses the Log4j program, and it was observed that simply entering a specific message could enable remote control of the user’s computer. Exploiting this could cause massive damage by attacking government agencies, companies, and financial institutions to implant malware.
Currently, it is unclear how many domestic financial companies use Log4j. Typically, the financial industry does not use free open-source software for security reasons. However, some financial institutions in Korea do use open-source software, so there is a possibility that Log4j has been applied. Only some developers responsible for operations know whether it is applied, making accurate status assessment difficult.
Unprecedented Vulnerability Prompts Security Firms and Government Agencies to Urge "Security Measures"
However, the Financial Security Institute explained that it is difficult to say that the recent attacks targeted specific financial company servers. It is more likely that hackers were attacking multiple servers to find vulnerable institutions, and financial companies were hit by the same attacks. A Financial Security Institute official said, "Lists of servers vulnerable to Log4j are being shared on hacking sites," adding, "(For domestic financial companies) detection is occurring, but vulnerabilities are rarely found so far."
As concerns about hacking targeting domestic IT companies, including financial firms, grow, local security companies are also moving quickly. East Security, developer of ALYac, has already posted related information on its blog since the 10th, when the vulnerability was first reported. An East Security official said, "Malicious files known to exploit the vulnerability can be detected and treated by the ALYac product."
AI security company Logpresso urgently released a scanner on GitHub to respond to the Log4j 2 vulnerability. A Logpresso official explained, "It currently supports temporary patches such as removing ‘JndiLookup.class’ as recommended in the Korea Internet & Security Agency’s security advisory."
Information security company AhnLab also posted warnings and update recommendations regarding the Log4j 2 vulnerability on its blog, urging caution. Currently, AhnLab’s TG/IPX, AIPS, and HIPS products can detect the vulnerability.
 Security update advisory announced on the 11th by the Korea Internet & Security Agency (KISA) on the 'Boho Nara' website. Photo by KISA website
Security update advisory announced on the 11th by the Korea Internet & Security Agency (KISA) on the 'Boho Nara' website. Photo by KISA website
Meanwhile, government agencies have also taken measures such as recommending emergency security updates after the vulnerability was discovered. On the 11th, the Ministry of Science and ICT requested urgent security measures according to the ‘Protect Nation Security Notice,’ warning that exploitation of the vulnerability could lead to malware and other damages.
They also emphasized prompt action for companies using the affected servers. Emergency notifications were sent to infrastructure providers, ISMS-certified companies (758 firms), CISOs (23,835 individuals), C-TAS (328 firms), cloud security-certified companies (36 firms), web hosting companies (477 firms), and IDCs (16 locations).
The Protect Nation Security Notice can be found as notice number 1614 in the KISA Protect Nation website’s resource center. For detailed information, inquiries can be made by calling 118 without an area code, where guidance on whether measures have been taken is also provided.
© The Asia Business Daily(www.asiae.co.kr). All rights reserved.